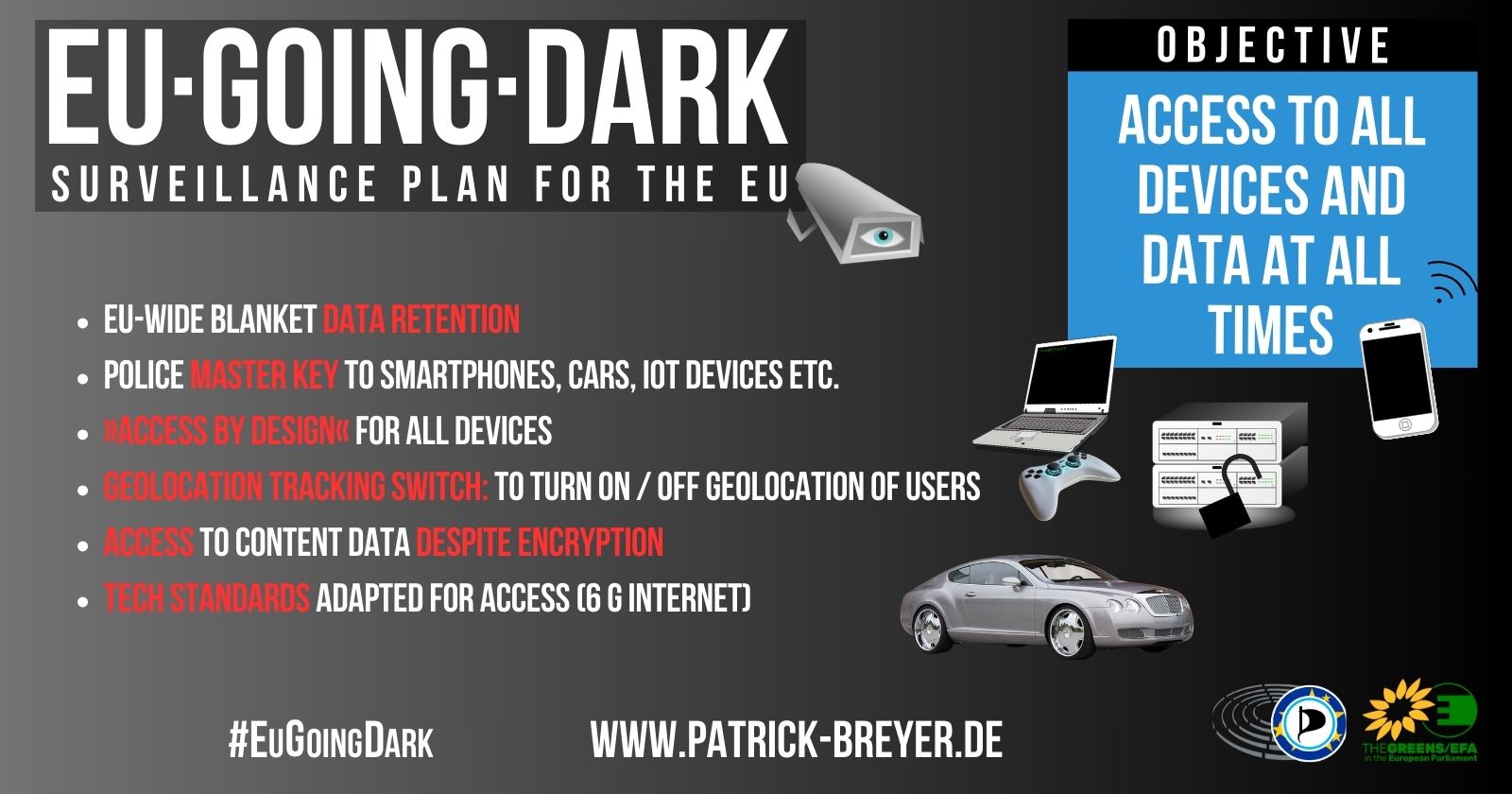
Anti-encryption EU expert group to make access to data a political and technical standard
The EU released a paper on the Commission’s plan for an expert group to replace end-to-end encryption and anonymity by law enforcement access (also known as the “Going Dark” program). The “Security by Design” concept is intended to ensure full law enforcement surveillance capabilities in legislation and technical standards.
EU lawmaker Patrick Breyer (Pirate Party / Greens/EFA ) comments:
“I call on the EU Commission to stop this anti-encryption and anti-anonymity working group at once! This is an attack on everything that keeps us safe online. The right to encryption protects whistleblowers, human rights defenders, pro-democracy activists and in fact all citizens from prosecution and harm. The right to anonymity ensures free speech and access to information; it protects us from data breaches, identity theft and stalking.
‘Going dark’ is an anxiety disorder the security complex is suffering from. In truth law enforcement has never had as pervasive an access to our private lives and personalities as in the digital era. We have never lived as long and secure as we do today.
On the subject of indiscriminate communications data retention, we urgently need decisive political action to implement the court decisions that protect the confidential communications of millions of citizens. In particular, our identity on the Internet (IP addresses) must be private in principle, which is why I have drawn a clear red line here.”
“Security by Design”: Surveillance as a political and technical standard
According to the paper, the expert group is to contribute to integrating a law enforcement perspective in all relevant EU policies and actions”. This concept of “Security by Design” is to be fully explored, and the expert group is also to explore how security by design could be a standard requirement in the development of new technologies. Therefore a more intensive presence of representatives of law enforcement authorities in relevant international standardisation bodies is being considered. The following are mentioned: European Committee for Standardisation (CEN/CENELEC), the European Telecommunications Standards Institute (ETSI) and the 3rd Generation Partnership Project (3GPP) – a worldwide cooperation of standardisation bodies in the field of mobile communications. As relevant technologies mentioned in the paper are artificial intelligence, quantum computers, 5G, the Internet of Things and cryptocurrencies.
Focus on: Encryption, data retention, VPN, roaming, etc.
The document lists the most urgent areas of work for the expert group as: encryption, more precisely access to stored data and to digital communication, data retention, access to localisation data and roaming data as well as anonymisation including VPN and darknet. The group will be chaired by the Directorate-General for Migration and Home Affairs (HOME) in the European Commission and by representatives of the Member State holding the Council Presidency – which will be Spain from July to December 2023. The group will be composed of high-level representatives from EU countries, the Commission and relevant EU institutions and agencies. Representatives from academia, civil society and business will only be involved on a selective ad-hoc basis.
Study: Policing does not need complete access to everything from everyone
While the work of the expert group is guided by the so-called “going dark” assumption that crime will go undetected in the digital world, a study on the role of encryption in investigations comes to a different conclusion. This study shows that encryption plays an important role in criminal investigations. On the one hand, encryption hinders criminal investigations, but on the other hand, it also plays a practical role in improving investigations. The study concludes:
“[P]olice have always been dealing with crucial crime information stored in a memory t which they do not have direct access. We call that memory the human brain. Since the police cannot read that (they do not have a key) and the criminal may choose to remain silent, police have to think of all kinds of ways to bypass that security and/or get the key and/or trick someone into revealing the information. Now we have a computer that, like the criminal, says: you will not get in and I will not say anything. Then, as police, you must think of alternatives to deal with that. The police have always done that. So, what is really different now? ”